|
#1
| |||
| |||
|
Can you please give me the past year question papers of DOEACC B Level Course Operating Systems Exam as it is very urgent for me?
|
|
#2
| ||||
| ||||
|
As you want to get the past year question papers of DOEACC B Level Course Operating Systems Exam so here is the information of the same for you: C3-R3: OPERATING SYSTEMS Time: 3 Hours Total Marks: 100 1. a) Does a process incur more execution overhead compared to a thread? Justify your answer. b) Distinguish between multiprocessing and multiprogramming. c) What are the “special files” in Unix? d) What is the main difference between worm and virus? e) State the practical limitations of implementing non-preemptive SJF algorithm. f) What is the difference between a long-term scheduler and a short-term scheduler? g) How can a single copy of a text editor be used to serve multiple users in a time-sharing system? (7x4) 2. a) What is TLB? Find out the effective memory-access time with an 80% hit ratio and the following access times: TLB access time: 20ns; MM access time: 100ns b) Describe the public-key encryption scheme and mention how is it advantageous to the data-encryption standard. (8+10) 3. Consider the following page reference during a given time interval for a memory consisting of 5 frames: y,c,z,c,d,a,y,a,e,a,y,f,d,e. Using the i) FIFO replacement strategy and ii) the LRU replacement strategy compare the results. Repeat both FIFO and LRU replacement strategies for memory with 3 frames and same page reference pattern. Comment on the findings and draw a conclusion justifying the adoption of a particular replacement strategy. (18) 4. a) What does ‘init’ do? What happens to the parent process id of a child when the parent terminates before its child? When does a child become ‘zombie’? b) With reference to Unix when do the following situations occur? i) Single process table entry contains pointers to the same file table entry. ii) Different file table entries point to the same i-node table entry. iii) Shell ‘forks’ a copy of itself and ‘waits’ for the child to terminate. c) How does CPU time-slice affect the Round-Robin algorithm? (8+6+4) 5. a) Show and explain an implementation of the classical producer-consumer (producer produces an item, keeps it in a buffer from where the consumer is picking it up) problem using semaphore. 1. Answer question 1 and any FOUR questions from 2 to 7. 2. Parts of the same question should be answered together and in the same sequence. b) What is dynamic loading? Mention its advantage. How is dynamic linking performed? Mention any disadvantage that you can think of for both the schemes. (10+8) 6. a) What is meant by a domain and the rights on it? Describe a Capability list and ways of protecting it from user tampering. b) Rewrite the following code introducing code parallelism wherever applicable: For i = 1 to k a(i) = b(i) + c(i) For j = 1 to k d(j) = x(j) – y(j) For p = 1 to k x(p) = y(p) + b(p) read(m,n,o,r) q = m*n + r/o write(q) c) Using preemptive SJF(shortest-job-first) algorithm draw the Gannt chart and calculate the average waiting time for the following processes: Process Arrival time Burst time P0 0 6 P1 2 4 P2 3 10 P3 7 9 (9+4+5) 7. a) Where and how “bit vector/table” is used? What are the advantages and disadvantages of the technique? b) What is deadlock? How can deadlock be prevented by not allowing “Hold and Wait” ? Is it a feasible policy? c) How can synchronization be achieved when two processes communicate by message passing? d) Provide a programming example of multithreading giving improved performance over a single-threaded solution. (5+5+5+3) 1. a) Differentiate between interrupts and exceptions. b) How can one detect that a message is lost during Inter Process Communication? c) What is the use of swap space? How can it be created in UNIX? d) Distinguish between a virus and a worm. e) Access Matrix is used for user authentication which can be implemented by Access List and Capability List. Briefly explain the two implementations. f) How can an user access a file located at remote UNIX server? g) What are the advantages of distributing execution of entire process or a part of it at different sites in a distributed operating system? (7x4) 2. a) Which are the possible events that may occur when a process is being executed by CPU? b) When does a process terminate? Which system call is used to terminate a process? Under what circumstances a parent process terminates a child process? c) Define Deadlock. Which are the conditions that should hold simultaneously in a system for a deadlock situation? (4+6+8) 3. a) Describe the problems with contiguous allocation method for allocating disk space. How does linked allocation method overcome the disadvantages of contiguous allocation method? b) Explain External Fragmentation. How the compaction can be used to solve the problem of external fragmentation? c) What is a thrashing? How can the problem of thrashing be prevented? d) The linux kernel does not allow paging out of kernel memory. Give one advantage and one disadvantage of this design decision. (4+4+4+6) 4. a) Distinguish between different divisions of classification as per US Department of Defence Trusted Computer System Evaluation Criteria. b) A disk drive has 5000 cylinders, numbered 0 to 4999. The drive is currently serving a request at cylinder 143, and the previous request was at cylinder 125. The queue of pending requests in FIFO order is 86, 1470, 913, 1774, 948, 1509, 1022, 1750, 130. Starting from the current head position, what is the total distance (in cylinders) that the disk arm moves to satisfy all the pending requests for FCFS, SSTF, SCAN, LOOK, disk scheduling algorithms? (6+12) 1. Answer question 1 and any FOUR questions from 2 to 7. 2. Parts of the same question should be answered together and in the same sequence. 5. a) Consider a system with five processes P0 through P4 and three resource types X,Y, Z. Following is the snapshot of system: Allocation Max Available X Y Z X Y Z X Y Z P0 0 1 0 7 5 3 3 3 2 P1 2 0 0 3 2 2 P2 3 0 2 9 0 2 P3 2 1 1 2 2 2 P4 0 0 2 4 3 3 Answer the following questions: i) State the Safety algorithm and Resource-Request algorithm. ii) Is the system in a safe state? b) What are the disadvantages of First Come First Serve and Shortest Job First scheduling algorithm? c) Suppose that the following processes arrive for execution at the times indicated. Each process will run the listed amount of time. Assume non-preemptive scheduling. Process Arrival Time Burst Time P1 0.0 8 P2 0.4 4 P3 1.0 1 What is the average turnaround time for these processes with the FCFS scheduling algorithm? d) A CPU scheduling algorithm determines an order for the execution of its scheduled processes. Given n processes to be scheduled one processor, how many possible different schedules are there? Give a formula in terms of n. (6+4+4+4) 6. a) Consider the following page reference string: 1, 2, 3, 4, 2, 1, 5, 6, 2, 1, 2, 3, 7, 6, 3, 2, 1, 2, 3, 6 How many page faults would occur for the LRU page replacement algorithm, assuming three frames? b) When do page faults occur? Describe the actions taken by the operating system when a page fault occurs c) Differentiate between logical address and physical address. (8+6+4) 7. a) Define a Distributed File System. Explain location transparency and location independence. Consider a user on ‘site A’ that wants to access data on ‘site B’. How the situation is handled by Network Operating System and Distributed Operating System? b) In a distributed system employing caching mechanism, a client machine is faced with the problem of deciding whether locally cached copy of the data is consistent with master copy. Which two approaches are used to verify the validity of cached data? c) What are the key design issues that must be dealt with in building a distributed operating system? (8+8+2) 1. a) What are the basic functions of an operating system? b) Differentiate between monitor mode and user mode with respect to protection (security) in a computer system. c) Explain Peterson’s solution for avoiding race condition. d) Explain in detail the structure of PCB. e) What is a thread? How are thread implemented in Kernel mode? f) What is the cause of thrashing? How does the system detect thrashing? Once it detects thrashing, what can the system do to eliminate this problem? g) List four modules of an operating system and explain in detail of functionality of each module. (7x4) 2. a) Suppose that a disk drive is currently serving a request at cylinder 11. The queue of pending requests in FIFO order is 98, 183, 37, 122, 14, 124, 65 and 67. Starting from the current head position, what is the total distance that the disk arm moves to satisfy all the pending requests, for each of the following disk-scheduling algorithm? i) FCFS ii) SSTF iii) SCAN/Elevator b) Distinguish between internal and external fragmentation. Provide any two solutions to avoid external fragmentation. c) What is a Deadlock? How can it be prevented? (9+5+4) 3. a) Consider a 'claim matrix', an 'allocation matrix' and a 'available vector' for a set of processes. Answer the following questions using the Banker’s algorithms: i) What are the maximum units of all resources? ii) What are the contents of the matrix need? iii) Is the system in a safe state? iv) A resource request for one of the processes is given. For example, if process P3 request 1 unit of R3, is this request be granted? If yes, give a all processes can run to completion. Claim Matrix Allocation Matrix Available Vector R1 R2 R3 R1 R2 R3 R1 R2 R3 P1 3 2 2 P1 1 0 0 1 1 2 P2 6 1 3 P2 5 1 1 P3 3 1 4 P3 2 1 1 P4 4 2 2 P4 0 0 2 1. Answer question 1 and any FOUR questions from 2 to 7. 2. Parts of the same question should be answered together and in the same sequence. b) What is a semaphore? Which are operations done on semaphore? Give implementation of producer-consumer problem with bounded buffer using semaphore. c) What is the difference between system call and system program. (10+6+2) 4. a) Explain contiguous allocation and linked list allocation for implementing file storage. b) What are the various layers of I/O software? Explain the function of each layer. c) What are the advantages of a Distributed File System over a file system in a centralized system? (6+6+6) 5. a) Draw and explain a process state transition diagram with one suspended state. b) Discuss swapping in brief. How does buddy system speed up merging when process swaps out? c) Consider the following set of processes in order P1, P2, P3, P4 and P5 with the length of the CPU burst time given in milliseconds. Their priorities are 3,5,2,1 and 4 respectively, with 5 being the highest priority, calculate average waiting time and turn-around time using following scheduling algorithms. (1) Shortest Remaining Time First (2) Round Robin (q=2) (3) Shortest Job First (4) Priority Scheduling (Preemptive) Process Arrival Time Burst Time P1 0 10 P2 1 9 P3 2 6 P4 3 7 P5 4 4 (5+5+8) 6. a) Explain the protection domain in UNIX. b) Discuss interleaving in brief. How does DMA increase system concurrency? c) How long does it take to load 64 Kbyte program from a disk whose average seek time is 10 msec, rotation time is 10 msec and track holds 32 Kbytes. Calculate time when page size is 2 Kbyte and also when page size is 4 Kbyte. Assume that pages are spread around the disk and no two pages are on the same cylinder. d) What information is saved and restored during a context switch? (6+6+4+2) 7. a) What is a page fault? What are the steps to be followed by operating system after occurring page fault? b) Explain the following terms: i) Spooling ii) Belady’s Anomaly iii) Priority Inversion Problem iv) Shared Pages c) Explain architecture of UNIX Operating System. (6+8+4) 1. a) List two salient features of each of the following types of systems: i) Multiprogramming ii) Multiprocessing iii) Time Sharing iv) Real Time Systems b) What is the use of shell in the operating system? List various types of shell available in UNIX? c) State the advantages of segmentation over paging. d) How an access matrix is used for implementing protection policies? e) Is mode switching the same as context switching? Give reasons for your answer. f) Operating system is also called Resource manager. Why? How are interrupts handled by the operating system? g) Explain short-term, medium-term and long-term scheduling. (7x4) 2. a) Explain, how Test and Set Lock instruction provides mutual exclusion for busy waiting. b) What is the difference between program and process? Explain various states in the life of a process. c) Five batch jobs A through E, arrive at a computer center at almost the same time. They have estimated running times of 10, 6, 2, 4 and 8 minutes. Their (externally determined) priorities are 3, 5, 2, 1, and 4, respectively, with 5 being the highest priority. For each of the following scheduling algorithms, determine the mean process turnaround time. Ignore process-switching overhead. 1) Round robin (Time quantum = 2) 2) Priority scheduling 3) Shortest job first For (1), assume that the system is multi-programmed, and that each job gets its fair share of the CPU. For (2) and (3), assume that only one job at a time runs, until it finishes. All jobs are completely CPU bound. (4+5+9) 3. a) Explain the term ‘Cycle Stealing’ in the context of DMA operations. b) What is meant by device independent I/O software? c) Explain how the "/proc" abstraction has evolved in Linux compared to other Unix implementations. d) What do you understand by reentrant code? How does it support sharing? (2+4+6+6) 1. Answer question 1 and any FOUR questions from 2 to 7. 2. Parts of the same question should be answered together and in the same sequence. 4. a) Given memory partitions of 100K, 500K, 200K, 300K and 600K (in order). How would each of the First-fit, Best-fit and Worst-fit algorithms place processes of 212K, 417K, 112K and 426K (in order)? Which algorithm makes the most efficient use of memory? b) Distinguish between internal fragmentation and external fragmentation. Which of the two is prevalent in paging system? c) What is the cause of thrashing? How can the OS reduce the effects of thrashing and improve overall performance? d) What is the difference between a block special file and a character special file? (6+4+4+4) 5. a) What is the process scheduling scheme used in Unix? b) Consider the following page reference string. 1, 2, 3, 4, 5, 3, 4, 1, 6, 7, 8, 9, 7, 8, 9, 5, 4, 5, 4, 2 How many page faults would occur for the following replacement algorithms for five frames? 1) LRU Replacement 2) FIFO Replacement (6+12) 6. a) Differentiate between deadlock detection, avoidance and prevention? Compare each on efficiency, safety and runtime cost parameters. b) Disk requests are received by the disk driver for cylinders 10, 22, 20, 2, 40, 6 and 38, in that order. A seek takes 6 msec per cylinder move. How much seek time is needed for 1) First Come First Served 2) Elevator algorithm (initially moving upwards) In both cases, the arm is initially at cylinder 20. (8+10) 7. a) What are the advantages and disadvantages of distributed system over centralized system? b) Explain transparency design issue in a Distributed operating system. c) How can the storage systems in a computer system be organized in a hierarchy? What is the use of the cache memory? Is it advisable to have more registers instead of the cache memory? Justify. (6+6+6) Contact Details: National Institute of Electronics and Information Technology Electronics Niketan, 6 CGO Complex, Jawaharlal Nehru Stadium Marg, CGO Complex, Pragati Vihar, New Delhi, Delhi 110003 011 2436 3330 India Map Location:
__________________ Answered By StudyChaCha Member |
|
#4
| |||
| |||
|
The ‘B’ level course of Department of Electronics Accreditation of Computer Courses (DOEACC) Society is equivalent to a MCA Degree which is recognized by the Ministry of Human Resource Development, Government of India. There are 5 semesters in this level Syllabus: Operating systems is a 60 hour course. In the first 8 hour an overview is given. Then the course will teach Process Management, Storage Management, I/O Systems Distributed Systems Protection & Security. At the end there will be a 6 hours of Case Study. Time Duration: The exam is for 3 hours and is carried during the month of July and January. Division of the paper: There are 5-6 questions in the paper which is subdivided into many small questions and the marks ranges from 4-10. Apart from the direct theoretical question, paper also contains numerical question which tests the application and the understanding part of the candidate. The paper covers the entire syllabus and student must mainly concentrate on ‘memory’ section. Here as per your demand I am providing you past year question papers of DOEACC B Level Course Operating Systems Exam Past year question papers of DOEACC B Level Course Operating Systems Exam 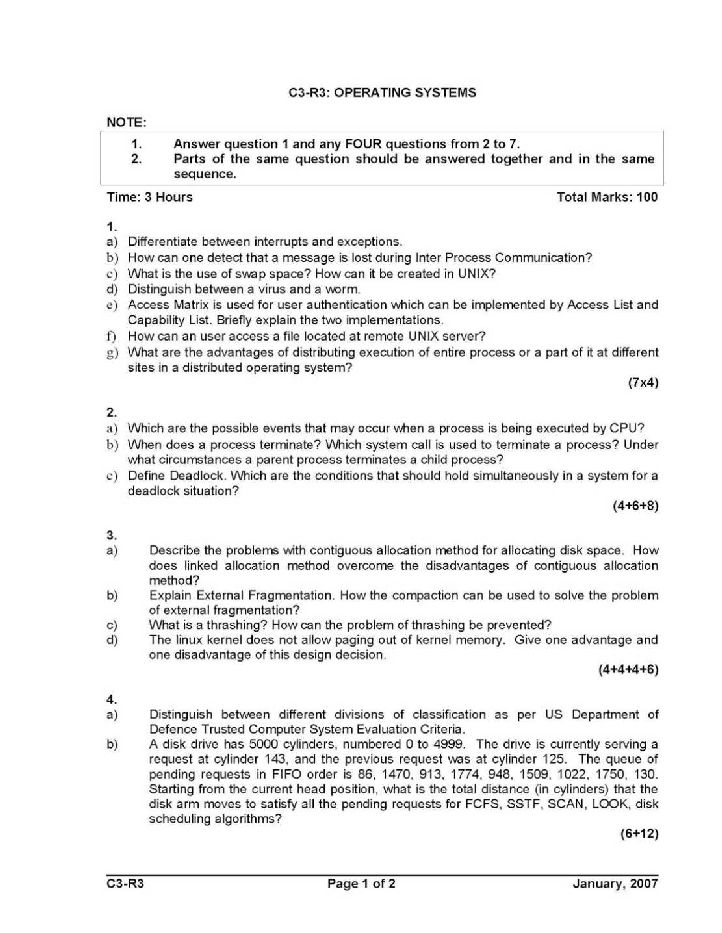  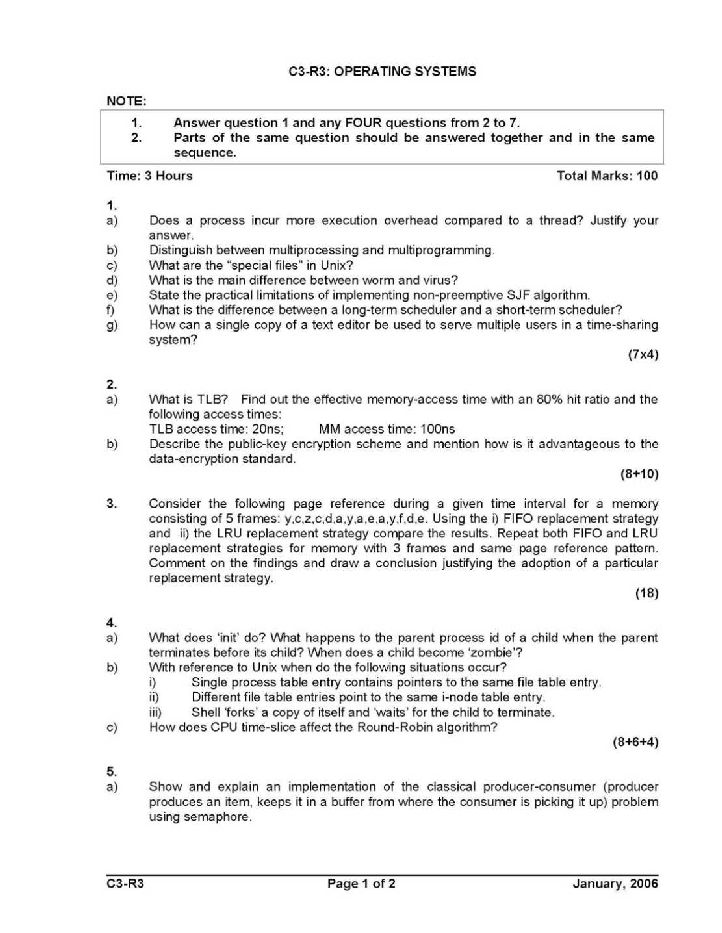 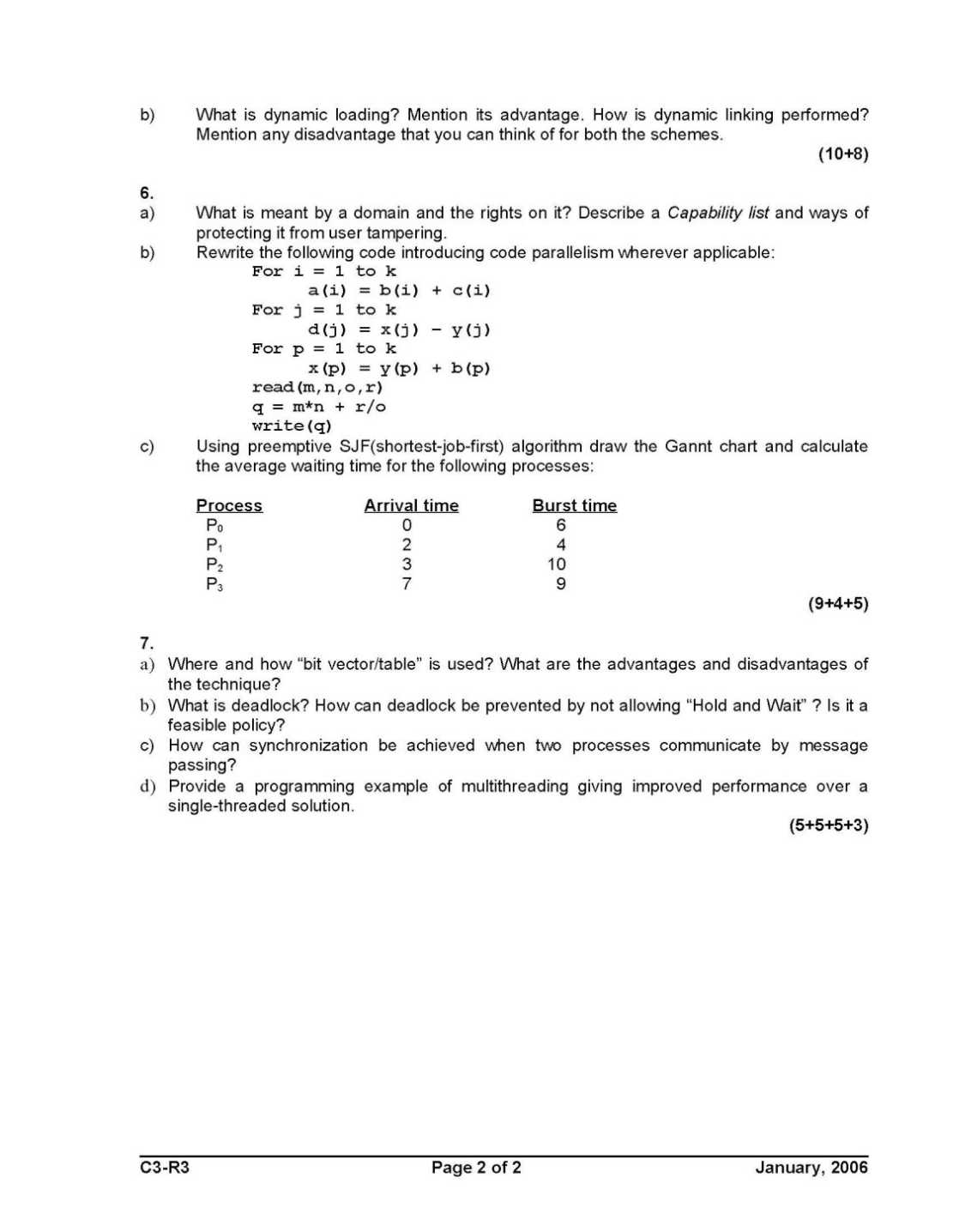
__________________ Answered By StudyChaCha Member |