|
#1
| |||
| |||
|
Can you give me question paper for GATE computer science and information technology engineering exam ?
|
|
#2
| ||||
| ||||
|
Here I am giving you question paper for GATE computer science and information technology engineering exam in PDF file attached with it .. 1. Consider an undirected random graph of eight vertices. The probability that there is an edge between a pair of vertices is ½. What is the expected number of unordered cycles of length three? (A) 1/8 (B) 1 (C) 7 (D) 8 Answer:-(C) 2. Which of the following statements is/are TRUE for undirected graphs? P: Number of odd degree vertices is even. Q: Sum of degrees of all vertices is even. (A) P only (B) Q only (C) Both P and Q (D) Neither P nor Q Answer:- (C) 5. Which one of the following expressions does NOT represent exclusive NOR of x and y? (A) xy x 'y' + (B) x y' Å (C) x ' y Å (D) x ' y' Å Answer: -(D) 8. Which of the following statements are TRUE? (1) The problem of determining whether there exists a cycle in an undirected graph is in P. (2) The problem of determining whether there exists a cycle in an undirected graph is in NP. (3) If a problem A is NP-Complete, there exists a non-deterministic polynomial time algorithm to solve A. (A) 1,2 and 3 (B) 1 and 2 only (C) 2 and 3 only (D) 1 and 3 only Answer: -(A) 9. Which of the following statements is/are FALSE? (1) For every non-deterministic Turing machine, there exists an equivalent deterministic Turing machine. (2) Turing recognizable languages are closed under union and complementation. (3) Turing decidable languages are closed under intersection and complementation (4) Turing recognizable languages are closed under union and intersection. (A) 1 and 4 only (B) 1 and 3 only (C) 2 only (D) 3 only Answer: -(C) 11. An index is clustered, if (A) it is on a set of fields that form a candidate key (B) it is on a set of fields that include the primary key (C) the data records of the file are organized in the same order as the data entries of the index (D) the data records of the file are organized not in the same order as the data entries of the index Answer:-(C)   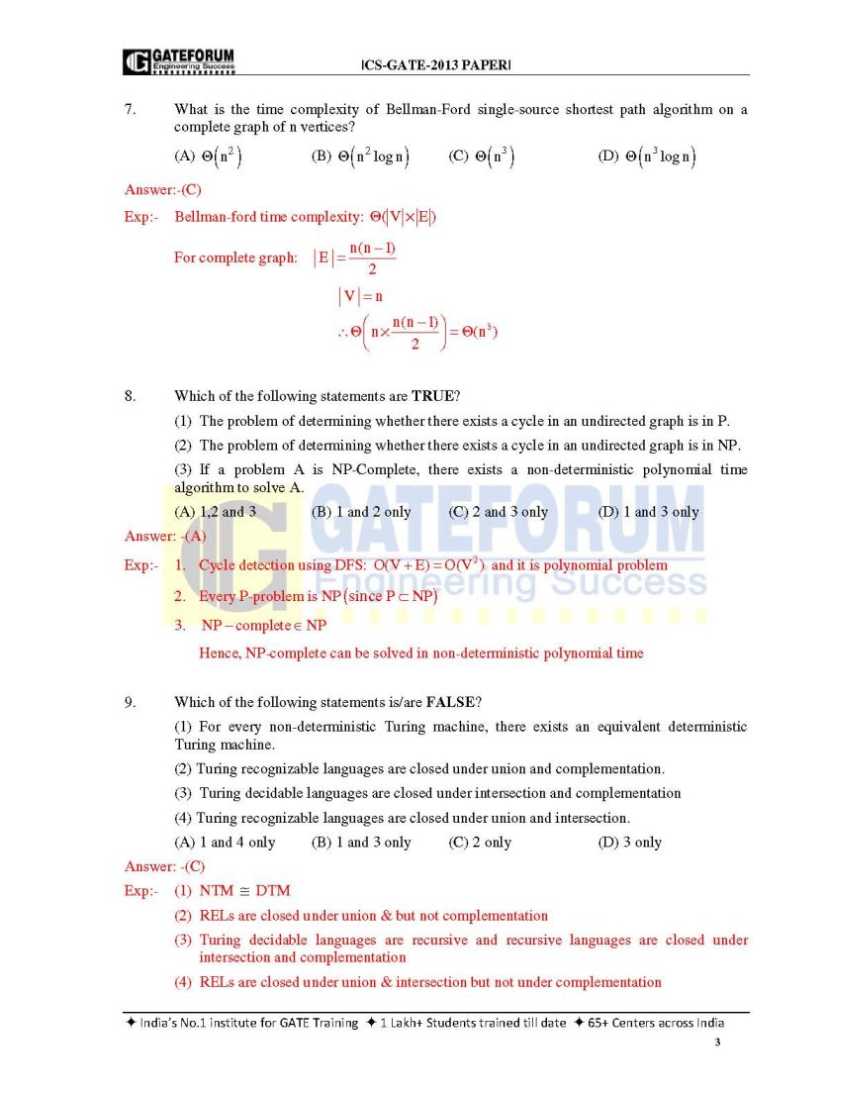 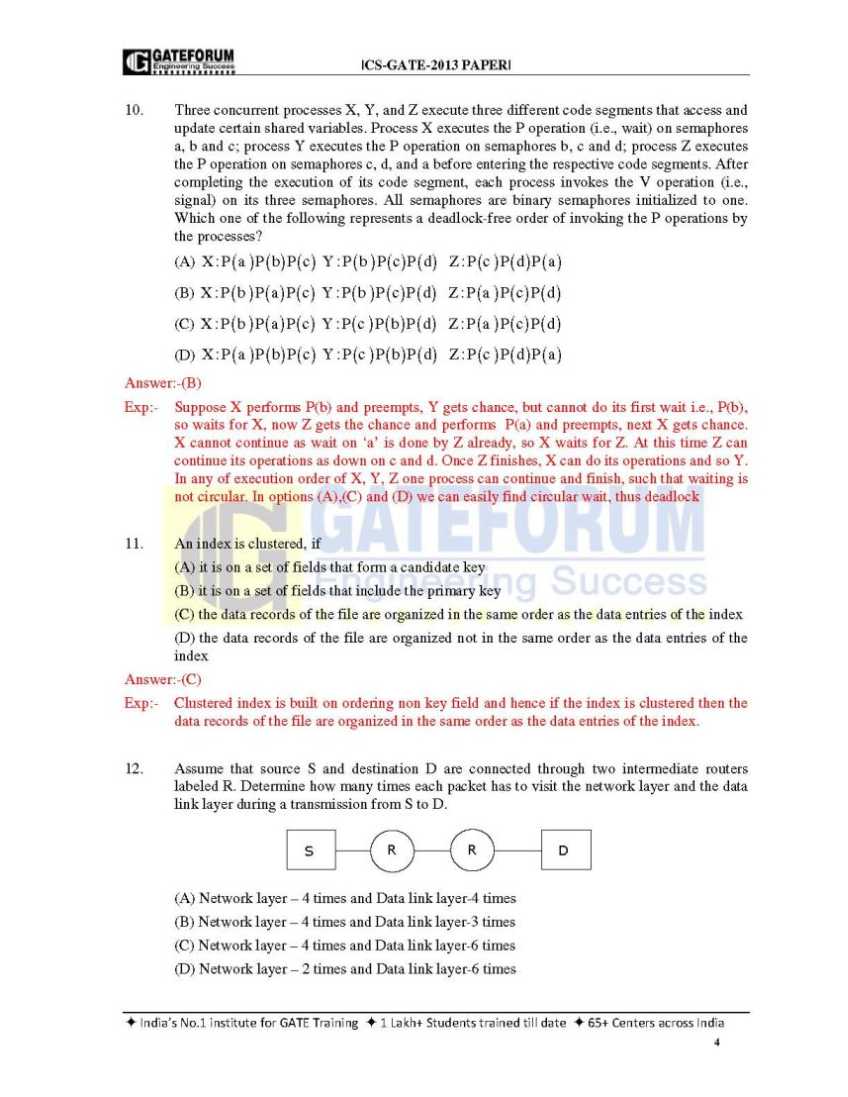
__________________ Answered By StudyChaCha Member |
|
#3
| |||
| |||
|
Here I am providing the GATE Syllabus of Computer Science and Information Technology for your idea . Digital Logic:Representation of signal by discrete bands of analog levels. It include topics- Logic functions, Minimization, Design and synthesis of sequential and combinational circuits; Number representation and computer arithmetic (floating and fixed point). Computer Organization and Architecture: It is the detail analysis of hardware and software of a computer It include topics-Machine instructions and addressing modes, data-path and ALU, CPU control design, I/O interface (DMA and Interrupt mode) , Main and cache memory, Secondary storage, Memory interface Instruction pipelining. Programming and Data Structures:It refers to coding and way of keeping things & arrange data in a systematic manner. It include topics- Programming in C ; Recursion, Functions , Parameter passing, Binding,Scope; Abstract data types, Arrays, Queues, Stacks, Linked Lists, Trees, Binary heaps,Binary search trees. Algorithms:It is the step by step procedure for performing a task. It include topics-Analysis, Asymptotic notation, Notions of time and space complexity, Worst and average case analysis; Design: Greedy approach, Divide-and-conquer ,Dynamic programming; Graph and tree traversals, Connected components, Shortest paths ,Spanning trees; Hashing, Searching,Sorting. Asymptotic analysis (worst, best, average cases) of space and Time, Lower and Upper bounds, Basic concepts of complexity classes NP,P, NP-complete,NP-hard. Theory of Computation:It is the branch that deals with whether an answer can be found to a problem and how well it can be solved using a step by step approach. It include topics-Regular languages and finite automata, Push-down automata and Context free languages , Turing machines and Recursively enumerable sets, Undecidability. Compiler Design: The compiler should be planned in such a manner that it has the ability to change the source program (in one programming language) into equivalent program (in another language). It include topics- Syntax directed translation,Parsing, Runtime environments, target and Intermediate code generation, Basics of code optimization; Lexical analysis. Operating System:Accumulation of softwares that supervises computer hardware. It include topics-Threads,Processes, Inter-process communication, Synchronization,Concurrency, Deadlock, CPU scheduling , File systems, I/O systems, Security and Protection, Memory management and virtual memory. Databases:It refers to accumulation of data in a systematic manner. It include topics-ER-model, Relational model ( tuple calculus,relational algebra), Database design ( normal forms,integrity constraints), File structures ( indexing,sequential files, B +and B trees), Query languages (SQL ),Transactions and concurrency control. Information Systems and Software Engineering  etail analysis of complimentary hardware and software that is use to regulate the information by people as well as organization.It include topics-information gathering, feasibility and requirement analysis,process specifications, input/output design, data flow diagrams, process life cycle, planning and managing the project, design, testing,coding, maintenance,Implementation. etail analysis of complimentary hardware and software that is use to regulate the information by people as well as organization.It include topics-information gathering, feasibility and requirement analysis,process specifications, input/output design, data flow diagrams, process life cycle, planning and managing the project, design, testing,coding, maintenance,Implementation.Computer Networks: Telecom.network by which data is being interchanged through computer.It include topics- ISO/OSI stack, LAN technologies ( Token ring,Ethernet ), Routing algorithms, Flow and error control techniques ,Congestion control, IP(v4), TCP/UDP and sockets, Application layer protocols ( dns, pop, http,ftp,smtp,icmp);Network security basic concepts of private and public key cryptography, digital signature, firewalls, Basic concepts of hubs, gateways,switches and routers. Web technologies:It helps to plan HTML pages. It include topics- basic concepts of client-server computing, XML & HTML. GATE Computer Science and Information Technology exam paper 1 In a population of N families, 50% of the families have three children, 30% of the families have two children and the remaining families have one child. What is the probability that a randomly picked child belongs to a family with two children? A) 3/23 B) 6/23 C) 3/10 D) 3/5 Answer : (B) 2 Which one of the following is NOT shared by the threads of the same process ? A) Stack B) Address Space C) File Descriptor Table D) Message Queue Answer : (A) 3 A subnet has been assigned a subnet mask of 255.255.255.192. What is the maximum number of hosts that can belong to this subnet? A) 14. B) 30 C) 62 D) 126 Answer : (C) 4 A software organization has been assessed at SEI CMM Level 4. Which of the following does the organization need to practice beside Process Change Management and Technology Change Management in order to achieve Level 5 ? A) Defect Detection B) Defect Prevention C) Defect Isolation D) Defect Propagation Answer : (B) 5 Suppose that two parties A and B wish to setup a common secret key (D-H key) between themselves using the Diffle-Hellman key exchange technique. They agree on 7 as the modulus and 3 as the primitive root. Party A chooses 2 and party B chooses 5 as their respective secrets. Their D-H key is A) 3 B) 4 C) 5 D) 6 Answer : (C) 6 We have two designs D1 and D2 for a synchronous pipeline processor. D1 has 5 pipeline stages with execution times of 3 nsec, 2 nsec, 4 nsec, 2 nsec and 3 nsec while the design D2 has 8 pipeline stages each with 2 nsec execution time. How much time can be saved using design D2 over design D1 for executing 100 instructions? A) 214 nsec B) 202 nsec C) 86 nsec D) -200 nsec Answer : (A) 7 Which of the following statements is FALSE regarding a bridge A) Bridge is a layer 2 device B) Bridge reduces collision domain C) Bridge is used to connect two or more LAN segments D) Bridge reduces broadcast domain Answer : (D) 8 What is the availability of a software with the following reliability figures? Mean Time Between Failure (MTBF) = 25 days Mean Time To Repair (MTTR) = 6 hours A) 1% B) 24% C) 99% D) 99.009% Answer : (B) 9 In a particular Unix OS, each data block is of size 1024 bytes, each node has 10 direct data block addresses and three additional addresses: one for single indirect block, one for double indirect block and one for triple indirect block. Also, each block can contain addresses for 128 blocks. Which one of the following is approximately the maximum size of a file in the file system? A) 512 MB B) 2 GB C) 8 GB D) 16 GB Answer : (D) 10 On a TCP connection, current congestion window size is Congestion Window = 4 KB. The window size advertised by the receiver is Advertise Window = 6 KB. The last byte sent by the sender is LastByteSent = 10240 and the last byte acknowledged by the receiver is LastByteAcked = 8192. The current window size at the sender is A) 2048 bytes B) 4096 bytes C) 6144 bytes D) 8192 bytes Answer : (B) 11 Which of the following statements is TRUE about CSMA/CD A) IEEE 802.11 wireless LAN runs CSMA/CD protocol B) Ethernet is not based on CSMA/CD protocol C) CSMA/CD is not suitable for a high propagation delay network like satellite network D) There is no contention in a CSMA/CD network Answer : (C) 12 How many pulses are needed to change the contents of a 8-bit upcounter from 10101100 to 00100111 (rightmost bit is the LSB)? A) 134 B) 133 C) 124 D) 123 Answer : (B) GATE Computer Science and Information Technology exam books     
__________________ Answered By StudyChaCha Member |
 |
| |